Wireshark Tutorial: Complete Network Traffic Analysis Guide
Wireshark is one of the most powerful and widely used network protocol analyzers. It allows you to capture and inspect network traffic in real time, making it an essential tool for cybersecurity professionals, ethical hackers, and network administrators.
What is Wireshark?
Wireshark is a free and open-source packet analysis tool that captures data traveling across a network. It helps users understand how devices communicate and allows deep inspection of network protocols.
How Wireshark Works
- Captures packets from a selected network interface
- Breaks down each packet into readable data
- Displays protocol, source, destination, and payload
- Allows filtering and detailed inspection
⚠️ Legal Notice
Only capture network traffic on networks you own or have permission to analyze. Unauthorized packet sniffing may violate privacy laws.
Wireshark Welcome Screen
Wireshark Welcome Screen:
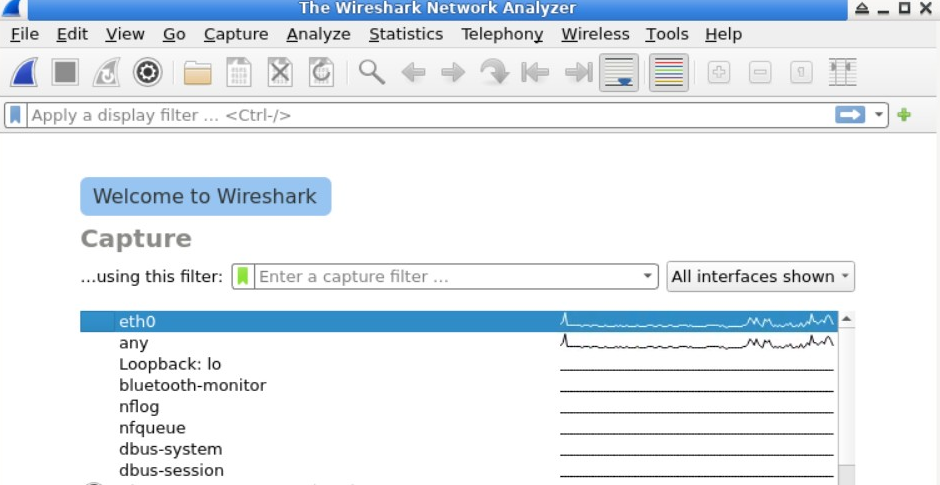
The welcome screen shows available network interfaces such as Wi-Fi or Ethernet. Selecting one will immediately start capturing packets.
Main Interface Components
Menu Bar
Access file options, settings, and export tools.
Toolbar
Quick controls for starting and stopping captures.
Display Filter Bar
Allows filtering of packets based on protocol or IP.
Packet List
Shows captured packets with details like time, source, and protocol.
Starting Packet Capture
Starting Packet Capture:
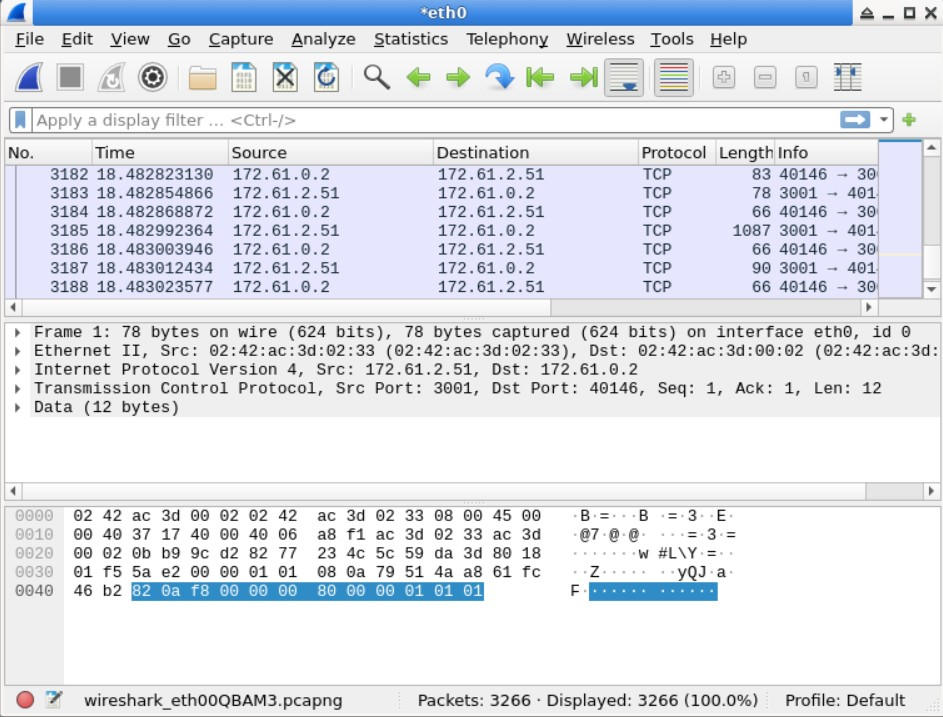
Select a network interface and Wireshark will begin capturing traffic instantly. You will see packets appearing in real time.
Understanding the Interface
Wireshark Interface:
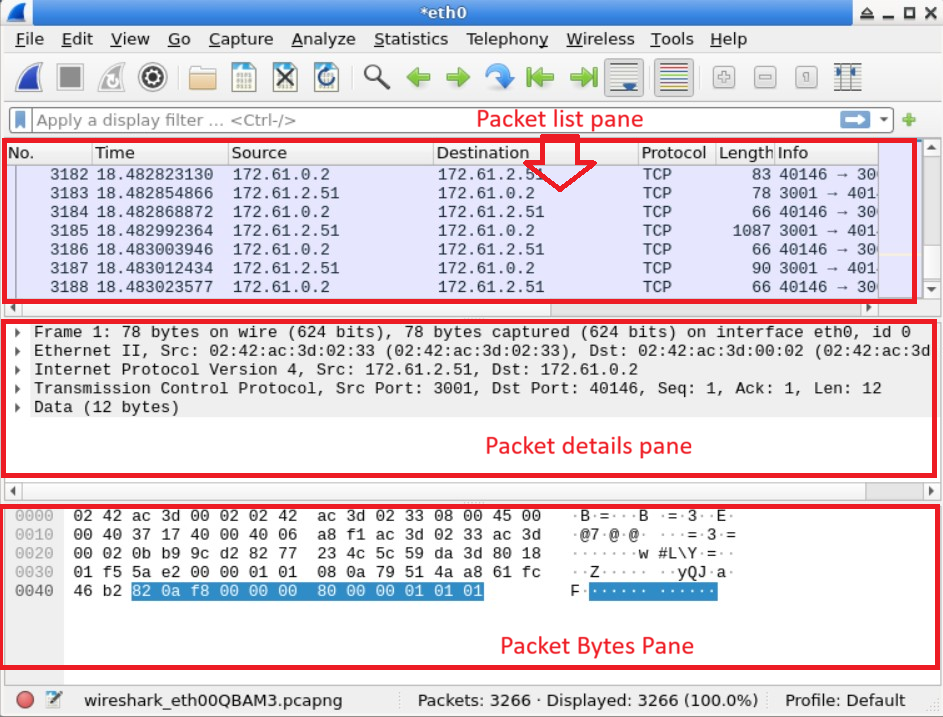
- Packet List Pane: Overview of captured packets
- Packet Details Pane: Structured breakdown
- Packet Bytes Pane: Raw hexadecimal data
Generating Traffic for Analysis
To analyze packets, you need traffic. A simple way is using the ping command:
This generates ICMP packets that Wireshark can capture.
Ping Requests:

Captured Packets:

Stopping Packet Capture
Stop Capture Button:

Click the red square button to stop capturing packets once enough data is collected.
Filtering Packets
Example filter:
This shows only ICMP packets.
Filtered Packets:

Real-World Scenario
A security analyst may detect suspicious traffic such as unknown connections or data leaks using Wireshark, helping prevent cyber attacks.
Common Mistakes
- Capturing too much data without filters
- Analyzing without understanding protocols
- Ignoring encrypted traffic limitations
Why Wireshark is Important
Wireshark helps detect attacks, troubleshoot networks, and understand how data flows across systems. It is essential for anyone learning cybersecurity.
FAQs
Is Wireshark legal?
Yes, when used ethically.
Can Wireshark capture passwords?
Only if data is not encrypted.
Is Wireshark beginner-friendly?
Yes, with practice.
Conclusion
Wireshark is a powerful tool for analyzing network traffic. Learning it provides deep insight into cybersecurity and network behavior.
Written by: PasswordGeeks Team